Web Architecture Quiz
Consider an on-line todo list:
ToDo List
Can you spot the problem with this design?
<h2>ToDo List</h2>
<ul>
<li>Buy milk <a href="/items/1/delete">[delete]</a></li>
<li>Feed dog <a href="/items/2/delete">[delete]</a></li>
</ul>
Web Architecture: HTML and HTTP
When this link is activated:
<a href="/items/1/delete">[delete]</a></li>
the client sends this:
GET /items/1/delete HTTP/1.1
Web Architecture: exploration is safe
People have certain expectations about questions as opposed to
statements or orders or requests. They apply to safe methods
in HTTP, such as GET:
| Customer |
Does that book come in paperback? |
Client |
GET /items/1/delete HTTP/1.1
|
| Seller |
We've charged $11.50 for that book to your credit card.
Nice doing business with you. |
Server |
200 OK
item 1 deleted
|
| Customer |
WHAT?! |
Client |
:-/ |
Web Architecture Quiz (Key)
Using HTTP as designed:
ToDo List
<h2>ToDo List</h2>
<form method="post" action="/update">
<ul>
<li>Buy milk <input type="checkbox" name="1" /></li>
<li>Feed dog <input type="checkbox" name="2" /></li>
</ul>
<p><input type="submit" value="Delete checked" /></p>
</form>
GET and POST: Innovation
|
Nov 1993
|
Changes and additions in this prerelease include:
- Implemented FORM METHOD="POST" with optional
ENCTYPE="application/x-www-form-urlencoded".
NCSA Mosaic for X 2.0 prerelease 8 available
Marc Andreessen (marca@ncsa.uiuc.edu)
Sun, 7 Nov 93 21:14:34 -0800
|
GET and POST: Rough Consensus and Running Code
 HTTP reaches Draft Standard status in the IETF, where
TCP/IP, DNS, and SMTP are standardized.
HTTP reaches Draft Standard status in the IETF, where
TCP/IP, DNS, and SMTP are standardized.
|
June 1999
|
... the GET and HEAD methods SHOULD NOT have the significance of taking an action other than retrieval. These methods ought to be considered "safe". This allows user agents to represent other methods, such as POST, PUT and DELETE, in a special way, so that the user is made aware of the fact that a possibly unsafe action is being requested.
9.1.1 Safe Methods of Hypertext Transfer Protocol -- HTTP/1.1
|
Web Architecture Volume 1
|
Dec 2004
|
Nadia's retrieval of weather information (an example of a read-only query or lookup) qualifies as a "safe" interaction; a safe interaction is one where the agent does not incur any obligation beyond the interaction. An agent may incur an obligation through other means (such as by signing a contract). If an agent does not have an obligation before a safe interaction, it does not have that obligation afterwards.
3.4. Safe Interactions in
Architecture of the World Wide Web, Volume One
|
Web Architecture: in practice
|
May 2005
|
So, the Google Web Accelerator prefetches links. Not a big
surprise. Unless clicking on a link destroys or alters data and you
can't figure out why your stuff is gone. This is not actually the web
accelerators fault.
37Signals and the Google Web Accelerator
|
|
Jun 2005
|
I've always known that using GETs when I should be using POSTs
wasn't kosher, but there were never any ramifications until now.
What Have We Learned From the Google Web Accelerator?
Chris Cantrell June 01, 2005
|
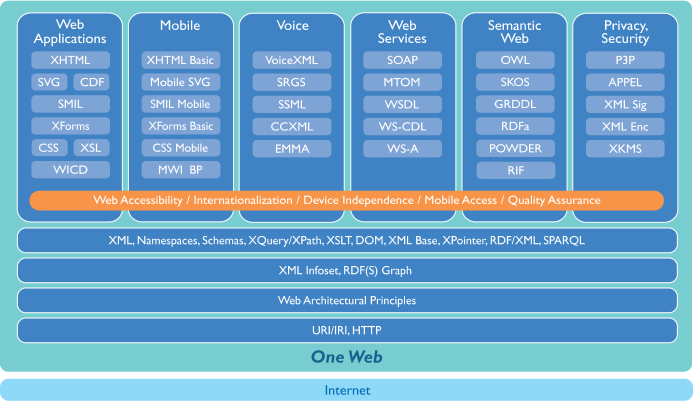
Web Architecture in W3C
The W3C Technical Architecture Group works on principles underlying
the 30 or 40 technologies W3C is developing.
How fast does W3C change?
Founded in 1994, we celebrated our 10th anniversary in 2004
and collected a historical
matierials for the event.
How fast does HTML change?
- Nov 1995: HTML 2.0 (IETF RFC 1866)
- Jan 1997: HTML 3.2 (W3C Recommendation)
Netscape's blink element and Microsoft's marquee element were omitted due to a mutual agreement between the two companies.
- Dec 1997: HTML 4.0 (W3C Recommendation)
- Dec 1999: HTML 4.01 (W3C Recommendation)
- Jan 2000: XHTML 1.0 (W3C Recommendation)
- Apr 2004: Web Applications 1.0 (WHATWG draft)
- Jan 2008: HTML 5 (W3C Working Draft)
How fast does the browser marketplace change?
Web Security: How fast do the bad guys make zombies?
Source: Zombie computer article in Wikipedia
Web Security: How fast do the bad guys make zombies?
The number of compromised zombie PCs in botnet networks has
quadrupled over the last three months, according to figures from the
Shadowserver Foundation. ... The clear trend within these figures is
upwards, with a rise in botnet numbers of 100,000 to 400,000 (if 30
day entropy is factored into equations) or from 20,000 to 60,000 (for
five day entropy).
Zombie network explosion
By John Leyden in The Register 2nd September 2008
How fast does the web change publishing?
There is no way to overstate what the dismemberment of The Star
means, adversely, to this metropolitan area.
Sadly, this event is of historic proportions
By: Steve
Rose, Publisher, KCCommunityNews.com Sep 3, 2008
- Where do Newspapers get their revenue?
- Advertisements
- Especially Classified Ads
Ads on the Web: Craigslist, Google
- Craigslist
- more than 30 million new classified ads each month
- price: $0 (except for New York real-estate)
Popular community web site Craigslist, which launched in the mid-1990s, has cost newspapers in the San Francisco Bay area from $50 million to $65 million in employment advertising revenue.
InformationWeek Dec 27 2004
- Google, Yahoo ads
- Newspaper ad price: $26 (per Thousand Impressions/ CPM)
- Internet: $6
- "Merrill Lynch expects a 2.6% gain in overall US advertising spend this year [2007] but anticipates that newspaper advertising will decline by 1.5%."
How fast does the Web change the free press?
How fast does the web
change government?
- First-time political candidate Sean Tevis needs "at least $26,000 to have a shot" in the KS race
- After two weeks of knocking on doors, he had collected
only $25
-
Web
comic went live July 16, and in a week and a half, he reached the
$26K goal.
Questions?
Follow-up resources:


 HTTP reaches Draft Standard status in the IETF, where
TCP/IP, DNS, and SMTP are standardized.
HTTP reaches Draft Standard status in the IETF, where
TCP/IP, DNS, and SMTP are standardized.
 1 Sep 2008: Official Google Blog: A fresh take on the browser, i.e Google Chrome
1 Sep 2008: Official Google Blog: A fresh take on the browser, i.e Google Chrome