Signatures and Namespaces
John M. Boyer
IBM Victoria Software Lab
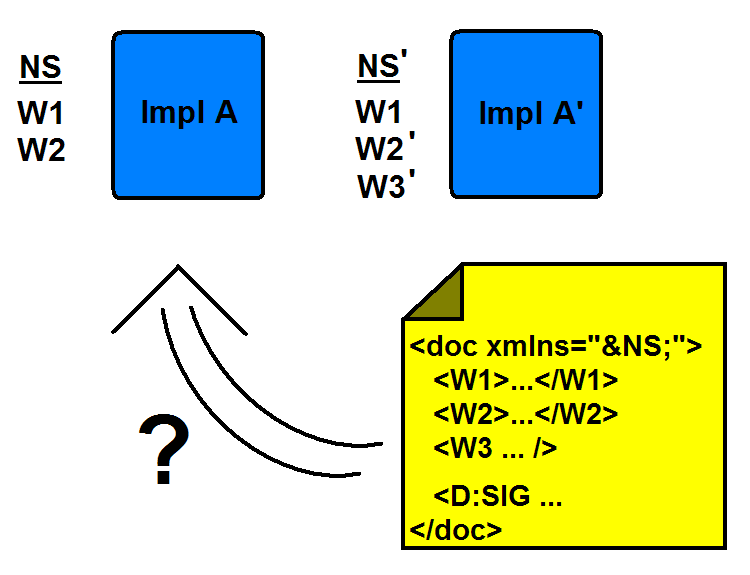
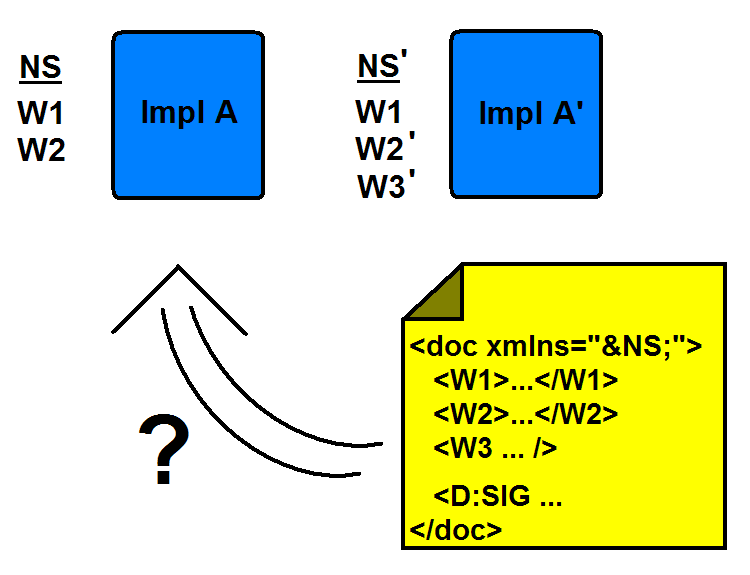
- Namespace starts out with just two words, W1 and W2.
- Build implementation that supports rendition of the vocabulary
- Later, requirements grow and shift
- Need to change meaning of W2 to W2'
- Need to add word W3
- Create new implementation to support new features
- Create document in new implementation containing W1, W2' and W3
- Sign document.
- Send document to user with original implementation
- Document validates, so it is "secure"
- User only sees or experiences W1 and W2 (original meaning, not primed meaning).
Typical software behavior is to ignore W3 as not understood.
- This is why namespace volatility corrupts signatures.
- Security experts throw out hash algorithms over significantly smaller infractions