2.
The
WebID
Protocol
Preconditions
2.1 Terminology
- Verification Agent
- Performs authentication on provided WebID credentials and determines if an Identification Agent can have access to a particular resource. A Verification Agent is typically a Web server, but may also be a peer on a peer-to-peer network.
- Identification Agent
-
Provides
identification
credentials
to
a
Verification
Agent.Agent . The Identification Agent is typically also a User Agent. - Identification Certificate
-
An
X.509
[
X509V3
]
Certificate
that
must
contain
a
Subject Alternative Nameextension with a URI entry. The URIshould be a URL, and should not be a URN. The URLidentifies the Identification Agent . TheURL mustURI should be dereference-able and result in a document containing RDF data. For example, the certificate would containhttp://example.org/webid#public, known as a WebIDURLURI , as theSubject Alternative Name:X509v3 extensions: ... X509v3 Subject Alternative Name: URI:http://example.org/webid#publicX509v3 extensions: ... X509v3 Subject Alternative Name: URI:http://example.org/webid#publicTODO: cover the case where there are more than one URI entry
-
WebID
URLURI -
A
URLURI specified via theSubject Alternative Nameextension of the Identification Certificate that identifies an Identification Agent . - public key
-
A
widely
distributed
crytographiccryptographic key that can be used to verify digital signatures and encrypt data between a sender and a receiver. A public key is always included in an Identification Certificate . - WebID Profile
-
A
structured
document
that
contains
identification
credentials
for
the
Identification
Agent
expressed
using
the
Resource
Description
Framework
[
RDF-CONCEPTS
].
Either
the
XHTML+RDFa
1.1
[
XHTML-RDFA
]
serialization
format
or
the
RDF/XML
[
RDF-SYNTAX-GRAMMAR
]
serialization
format
must
be
supported
by
the
mechanism,
e.g.
a
Web
Service,
providing
the
WebID
Profile
document.
Alternate
RDF
serialization
formats,
such
as
N3
[
N3
]
or
Turtle
[
TURTLE
],
may
be
supported
by
the
mechanism
providing
the
WebID
Profile
document.
Whether or not RDF/XML, XHTML+RDFa 1.1, both or neither serialization of RDF should be required serialization formats in the specification is currently under heavy debate.
2.2 Creating the certificate
The
user
agent
will
create
a
Identification
Certificate
with
a
Subject
Alternative
Name
URI
entry.
This
URI
must
be
one
that
dereferences
to
a
document
the
user
controls
so
that
he
can
publish
the
public
key
of
the
Identification
Certificate
at
this
URI.
For
example,
if
a
user
Joe
controls
http://joe.example/profile
,
then
his
WebID
can
be
http://joe.example/profile#me
explain why the WebID URI is different from the URI of the WebID profile document.
As an example to use throughout this specification here is the following certificate as an output of the openssl program.
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
5f:df:d6:be:2c:73:c1:fb:aa:2a:2d:23:a6:91:3b:5c
Signature Algorithm: sha1WithRSAEncryption
Issuer: O=FOAF+SSL, OU=The Community of Self Signers, CN=Not a Certification Authority
Validity
Not Before: Jun 8 14:16:14 2010 GMT
Not After : Jun 8 16:16:14 2010 GMT
Subject: O=FOAF+SSL, OU=The Community Of Self Signers/UID=https://example.org/profile#me, CN=Joe (Personal)
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Public-Key: (2048 bit)
Modulus:
00:cb:24:ed:85:d6:4d:79:4b:69:c7:01:c1:86:ac:
c0:59:50:1e:85:60:00:f6:61:c9:32:04:d8:38:0e:
07:19:1c:5c:8b:36:8d:2a:c3:2a:42:8a:cb:97:03:
98:66:43:68:dc:2a:86:73:20:22:0f:75:5e:99:ca:
2e:ec:da:e6:2e:8d:15:fb:58:e1:b7:6a:e5:9c:b7:
ac:e8:83:83:94:d5:9e:72:50:b4:49:17:6e:51:a4:
94:95:1a:1c:36:6c:62:17:d8:76:8d:68:2d:de:78:
dd:4d:55:e6:13:f8:83:9c:f2:75:d4:c8:40:37:43:
e7:86:26:01:f3:c4:9a:63:66:e1:2b:b8:f4:98:26:
2c:3c:77:de:19:bc:e4:0b:32:f8:9a:e6:2c:37:80:
f5:b6:27:5b:e3:37:e2:b3:15:3a:e2:ba:72:a9:97:
5a:e7:1a:b7:24:64:94:97:06:6b:66:0f:cf:77:4b:
75:43:d9:80:95:2d:2e:85:86:20:0e:da:41:58:b0:
14:e7:54:65:d9:1e:cf:93:ef:c7:ac:17:0c:11:fc:
72:46:fc:6d:ed:79:c3:77:80:00:0a:c4:e0:79:f6:
71:fd:4f:20:7a:d7:70:80:9e:0e:2d:7b:0e:f5:49:
3b:ef:e7:35:44:d8:e1:be:3d:dd:b5:24:55:c6:13:
91:a1
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Basic Constraints: critical
CA:FALSE
X509v3 Key Usage: critical
Digital Signature, Non Repudiation, Key Encipherment, Key Agreement, Certificate Sign
Netscape Cert Type:
SSL Client, S/MIME
X509v3 Subject Key Identifier:
08:8E:A5:5B:AE:5D:C3:8B:00:B7:30:62:65:2A:5A:F5:D2:E9:00:FA
X509v3 Subject Alternative Name: critical
URI:https://joe.example/profile#me
Signature Algorithm: sha1WithRSAEncryption
cf:8c:f8:7b:b2:af:63:f0:0e:dc:64:22:e5:8a:ba:03:1e:f1:
ee:6f:2c:f5:f5:10:ad:4c:54:fc:49:2b:e1:0d:cd:be:3d:7c:
78:66:c8:ae:42:9d:75:9f:2c:29:71:91:5c:29:5b:96:ea:e1:
e4:ef:0e:5c:f7:07:a0:1e:9c:bf:50:ca:21:e6:6c:c3:df:64:
29:6b:d3:8a:bd:49:e8:72:39:dd:07:07:94:ac:d5:ec:85:b1:
a0:5c:c0:08:d3:28:2a:e6:be:ad:88:5e:2a:40:64:59:e7:f2:
45:0c:b9:48:c0:fd:ac:bc:fb:1b:c9:e0:1c:01:18:5e:44:bb:
d8:b8
Should we formally require the Issuer to be O=FOAF+SSL, OU=The Community of Self Signers, CN=Not a Certification Authority. This was discussed on the list as allowing servers to distinguish certificates that are foaf+Ssl enabled from others. Will probably need some very deep TLS thinking to get this right.
discuss the importance for UIs of the CN
2.3 Publishing the WebID Profile Document
The
WebID
Profile
document
must
expose
the
relation
between
the
WebID
URI
and
the
Identification
Agent
's
public
key
s
using
the
cert
and
rsa
ontologies,
as
well
as
the
cert
or
xsd
datatypes.
The
set
of
relations
to
be
published
at
the
WebID
Profile
document
can
be
presented
in
a
graphical
notation
as
follows.
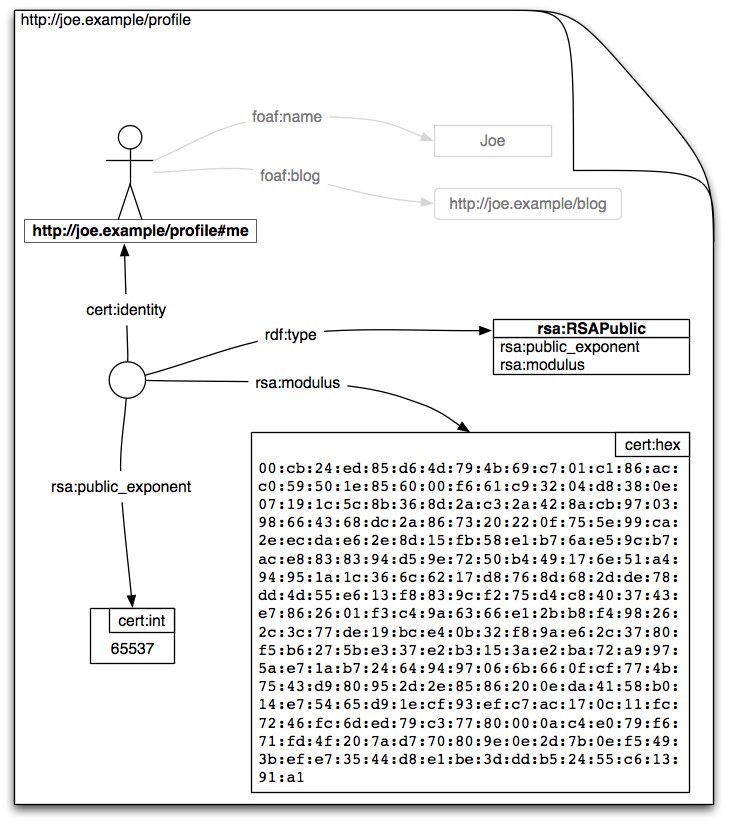
The document can publish many more relations than are of interest to the WebID protocol, as shown in the above graph by the grayed out relations.
The encoding of this graph is immaterial to the protocol, so long as a well known mapping to the format of the representation to such a graph can be found. Below we discuss the most well known formats, and a method for dealing with new unknown formats as they come along.
The WebID provider must publish the graph of relations in one of the well known formats, though he may publish it in a number of formats to increase the useabulity of his site using Content Negotations.
Add content negoatiation pointers
It is particularly useful to have one of the representations be in HTML or XHTML even if it is not marked up in RDFa as this allows people using a web browser to understand what the information at that URI represents.
2.3.1 Turtle
A widely used format for writing RDF graphs is the Turtle notation.
@prefix cert: <http://www.w3.org/ns/auth/cert#> .
@prefix rsa: <http://www.w3.org/ns/auth/rsa#> .
@prefix foaf: <http://xmlns.com/foaf/0.1/> .
@prefix : <https://joe.example/profile#> .
:me a foaf:Person;
foaf:name "Joe" .
[] a rsa:RSAPublicKey;
rsa:modulus """
00:cb:24:ed:85:d6:4d:79:4b:69:c7:01:c1:86:ac:
c0:59:50:1e:85:60:00:f6:61:c9:32:04:d8:38:0e:
07:19:1c:5c:8b:36:8d:2a:c3:2a:42:8a:cb:97:03:
98:66:43:68:dc:2a:86:73:20:22:0f:75:5e:99:ca:
2e:ec:da:e6:2e:8d:15:fb:58:e1:b7:6a:e5:9c:b7:
ac:e8:83:83:94:d5:9e:72:50:b4:49:17:6e:51:a4:
94:95:1a:1c:36:6c:62:17:d8:76:8d:68:2d:de:78:
dd:4d:55:e6:13:f8:83:9c:f2:75:d4:c8:40:37:43:
e7:86:26:01:f3:c4:9a:63:66:e1:2b:b8:f4:98:26:
2c:3c:77:de:19:bc:e4:0b:32:f8:9a:e6:2c:37:80:
f5:b6:27:5b:e3:37:e2:b3:15:3a:e2:ba:72:a9:97:
5a:e7:1a:b7:24:64:94:97:06:6b:66:0f:cf:77:4b:
75:43:d9:80:95:2d:2e:85:86:20:0e:da:41:58:b0:
14:e7:54:65:d9:1e:cf:93:ef:c7:ac:17:0c:11:fc:
72:46:fc:6d:ed:79:c3:77:80:00:0a:c4:e0:79:f6:
71:fd:4f:20:7a:d7:70:80:9e:0e:2d:7b:0e:f5:49:
3b:ef:e7:35:44:d8:e1:be:3d:dd:b5:24:55:c6:13:
91:a1
"""^^cert:hex;
rsa:public_exponent "65537"^^cert:int;
cert:identity :me .
2.3.2 RDFa HTML notation
There are many ways of writing out the above graph using RDFa in html. Here is just one example.
<html xmlns="http://www.w3.org/1999/xhtml"
xmlns:cert="http://www.w3.org/ns/auth/cert#"
xmlns:foaf="http://xmlns.com/foaf/0.1/"
xmlns:owl="http://www.w3.org/2002/07/owl#"
xmlns:rsa="http://www.w3.org/ns/auth/rsa#"
xmlns:rdf="http://www.w3.org/1999/02/22-rdf-syntax-ns#">
<head>
</head>
<body>
<h2>My RSA Public Key</h2>
<dl typeof="rsa:RSAPublicKey">
<dt>WebId</dt><dd href="#me" rel="cert:identity">http://joe.example/profile#me</dd>
<dt>Modulus (hexadecimal)</dt>
<dd property="rsa:modulus" datatype="cert:hex">
00:cb:24:ed:85:d6:4d:79:4b:69:c7:01:c1:86:ac:
c0:59:50:1e:85:60:00:f6:61:c9:32:04:d8:38:0e:
07:19:1c:5c:8b:36:8d:2a:c3:2a:42:8a:cb:97:03:
98:66:43:68:dc:2a:86:73:20:22:0f:75:5e:99:ca:
2e:ec:da:e6:2e:8d:15:fb:58:e1:b7:6a:e5:9c:b7:
ac:e8:83:83:94:d5:9e:72:50:b4:49:17:6e:51:a4:
94:95:1a:1c:36:6c:62:17:d8:76:8d:68:2d:de:78:
dd:4d:55:e6:13:f8:83:9c:f2:75:d4:c8:40:37:43:
e7:86:26:01:f3:c4:9a:63:66:e1:2b:b8:f4:98:26:
2c:3c:77:de:19:bc:e4:0b:32:f8:9a:e6:2c:37:80:
f5:b6:27:5b:e3:37:e2:b3:15:3a:e2:ba:72:a9:97:
5a:e7:1a:b7:24:64:94:97:06:6b:66:0f:cf:77:4b:
75:43:d9:80:95:2d:2e:85:86:20:0e:da:41:58:b0:
14:e7:54:65:d9:1e:cf:93:ef:c7:ac:17:0c:11:fc:
72:46:fc:6d:ed:79:c3:77:80:00:0a:c4:e0:79:f6:
71:fd:4f:20:7a:d7:70:80:9e:0e:2d:7b:0e:f5:49:
3b:ef:e7:35:44:d8:e1:be:3d:dd:b5:24:55:c6:13:
91:a1
</dd>
<dt>Exponent (decimal)</dt>
<dd property="rsa:public_exponent" datatype="cert:int">65537</dd>
</dl>
</body>
</html>
If a WebId provider would rather prefer not to mark up his data in RDFa, but just provide a human readable format for users and have the RDF graph appear in a machine readable format such as RDF/XML then he should publish the link from the HTML to the machine readable format as follows:
<html> <head> <link type="rel" type="application/rdf+xml" href="profile.rdf"/> </head> <body> ... </body> </html>
2.3.3 In RDF/XML
RDF/XML is easy to generate automatically from structured data, be it in object notiation or in relational databases. Parsers for it are also widely available.
TODO: the dsa ontology
2.3.4 In Portable Contacts format using GRDDL
TODO: discuss other formats and GRDDL, XSPARQL options for xml formats
summarize and point to content negotiation documents